Private Encryption for Schematic Review
Encrypt at Rest means your design files are encrypted before they leave your facility using industry-standard OpenSSL. Even though your connection to Tomachie is HTTPS/TLS 1.2, your plaintext design never travels over the network. Your design then sits encrypted on disk while it is decrypted to memory only for analysis. Your results are then encrypted to disk with your encryption key. Your decryption key is used ephemerally from the browser to decrypt your results when you, and only you, want to view them.
- Files encrypted with AES-256-CBC (same encryption used by banks and governments)
- Only you possess the decryption key
- Your key is used ephemerally during processing, then immediately discarded — never saved to disk
- Input files deleted immediately after processing
- Results remain encrypted at rest — you decrypt in your browser
- Even if our servers were breached, your designs remain encrypted
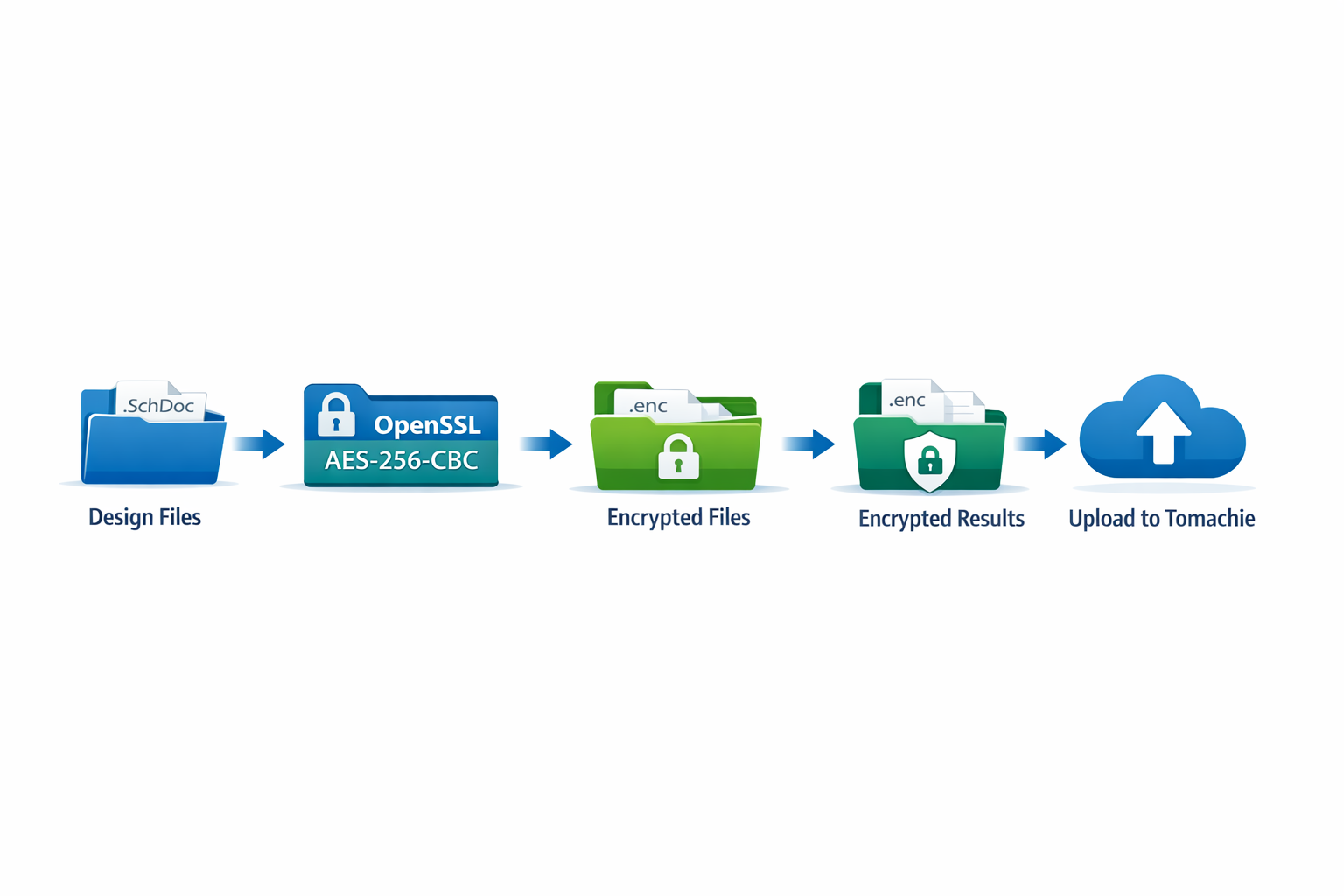
How It Works: Encryption Flow
You encrypt your design files locally before they ever leave your facility:
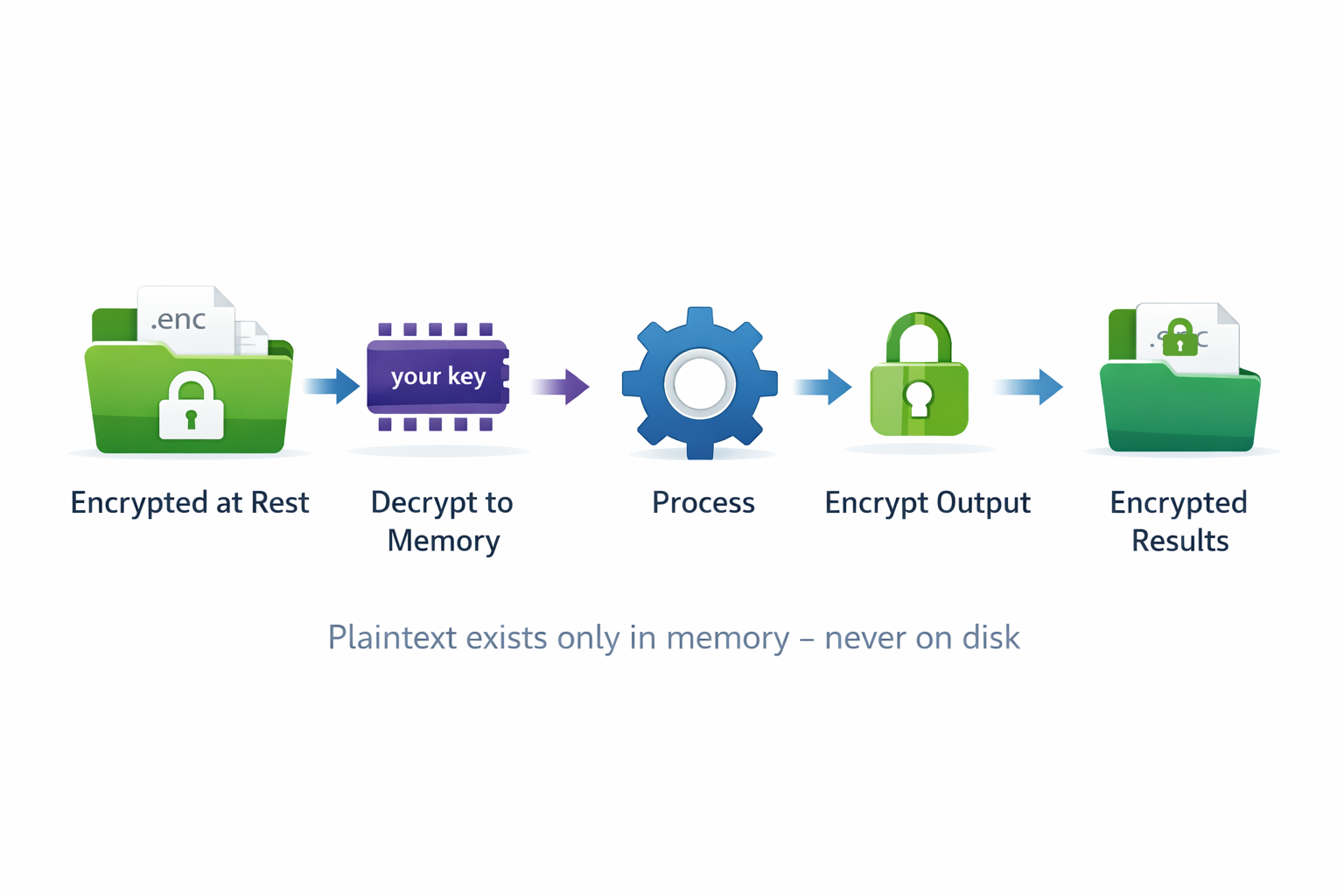
How It Works: Server Processing
On Tomachie servers, your files remain encrypted at rest. Decryption occurs only in memory during processing:
Security Properties
| Property | How It's Achieved |
|---|---|
| Encryption Standard | AES-256-CBC — 256-bit key. Same standard used by TLS 1.3, banking systems, and government classified networks. |
| At-Rest Encryption | Files remain encrypted on Tomachie servers at all times. Decryption occurs only in memory during processing. |
| Key Never Stored | Your encryption key is used ephemerally during processing then immediately discarded — it is never saved to disk. Only you have it. |
| Auditability | Uses OpenSSL — open source, extensively audited, FIPS 140-2 certified versions available. |
| Key Strength | 256-bit random key = 2256 possible combinations. Computationally infeasible to brute-force. |
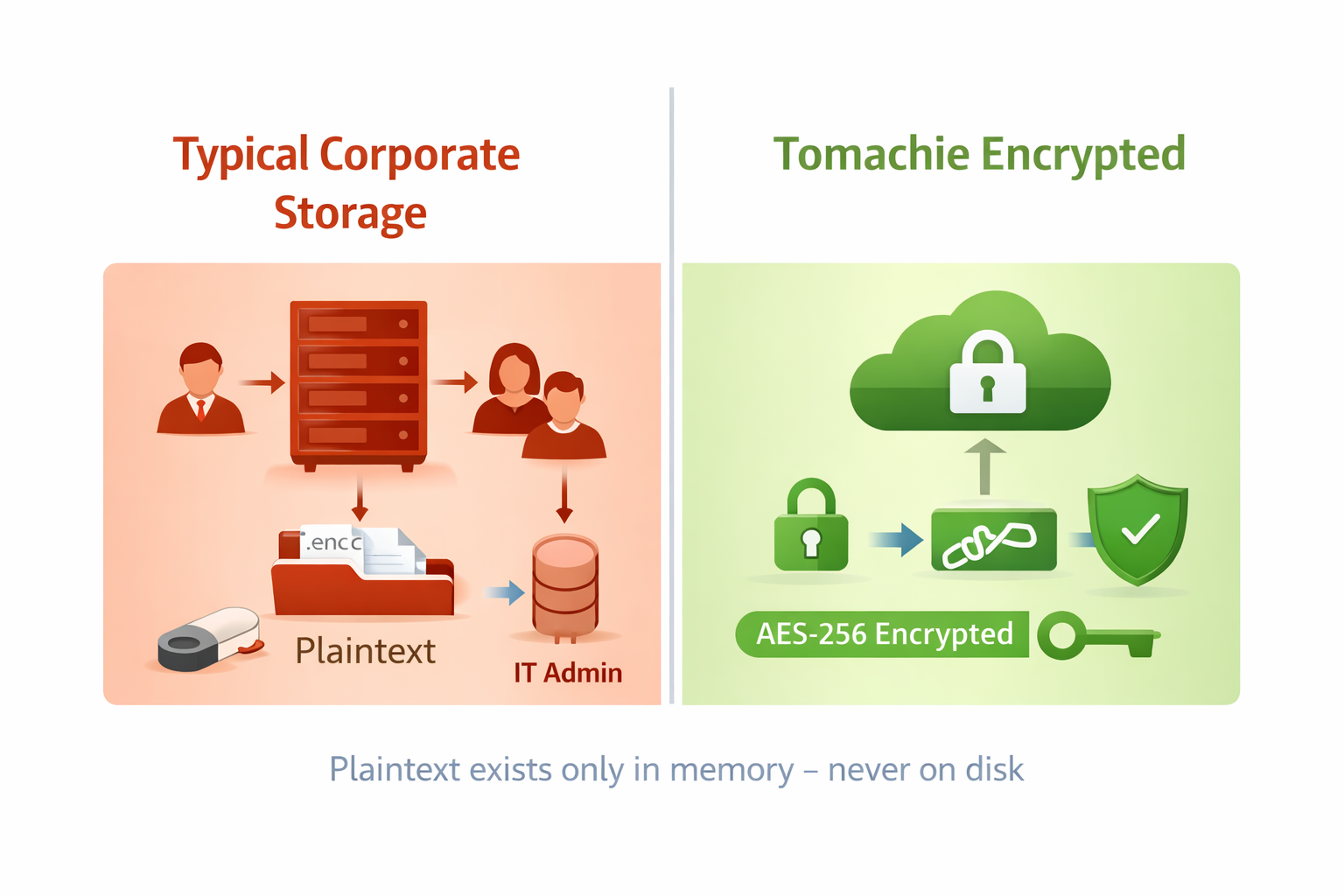
How Secure Are Your Files Today?
Consider how your design files are typically stored: on a shared server, a developer's laptop, or in cloud storage. In most organizations, these files sit in plaintext — accessible to anyone with network credentials.
Typical Corporate Storage
- Files in plaintext on shared drives
- Accessible to IT administrators
- Included in backup systems
- Network credentials = full access
Tomachie Private Encryption
- AES-256 encrypted before upload
- Only you hold the key
- Key used in memory, never stored
- Results encrypted at rest
Try It: Pre-Encrypted FPGA1394V3 Demo
This pre-encrypted sample uses the FPGA1394V3 design from our examples area. Follow these steps to experience the workflow:
- Download the encrypted ZIP file
- Open and inspect its contents —
- Upload to the Private Submit area — the demo key is provided there
What's Included
| Feature | Standard | With Token |
|---|---|---|
| Design analysis (DFT, JTAG, ERC) | Yes | Yes |
| AI-assisted review | Yes | Optional |
| Files encrypted at rest | — | Yes |
| Key never stored | — | Yes |
| Input files deleted immediately | — | Yes |
| Local encryption script | — | Yes |
Ready to encrypt your own designs?
After purchase, we provide a script for local private key generation and OpenSSL encryption of your design files.
Purchase Token — $10 per upload